Pegasus – Israel Spyware: How Infect Smartphone and Get Rid Of
 |
| Pegasus software - Photo Kashmir Reader |
What is Pegasus Spyware?
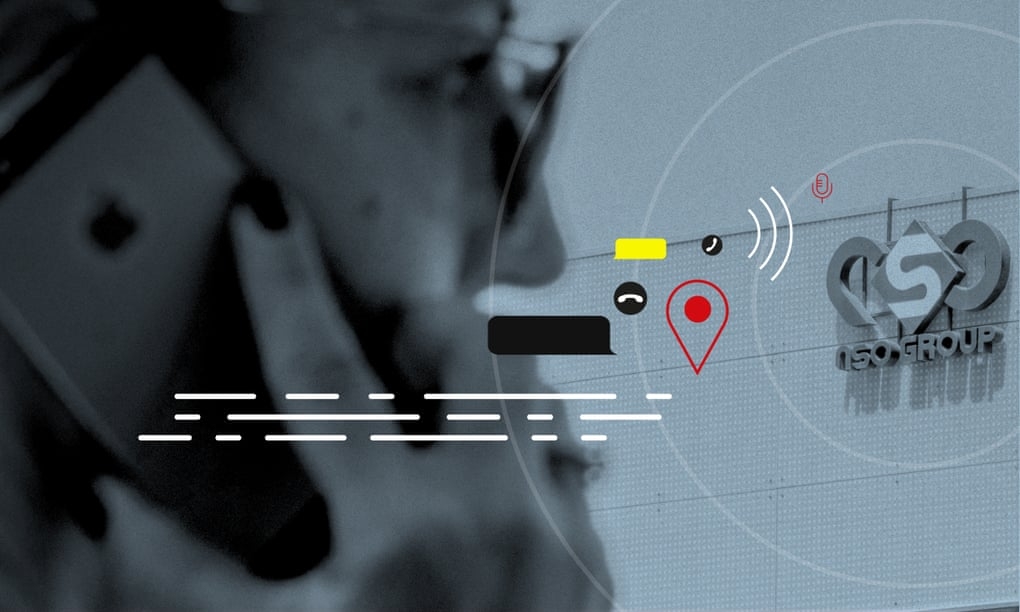
Pegasus is reportedly a highly invasive tool by NSO, the world's most infamous hacker-for-hire outfit. The firm's spyware is used to spy on people through their smartphones.
It works by sending an exploit link to the target user, which if clicked downloads malware or code onto the device without the user's knowledge or permission.
| The NSO Group is a private company based in Israel that is a leading maker of spyware. Its signature product, Pegasus, is designed to break into iPhones and Android devices. Founded in 2010, the company says it has 60 government customers in 40 countries. The company, which also has offices in Bulgaria and Cyprus, reportedly has 750 employees and recorded revenue of more than $240 million last year, according to Moody’s. It’s majority-owned by Novalpina Capital, a London-based private-equity firm.
|
Pegasus isn't supposed to be used to go after activists, journalists and politicians. "NSO Group licenses its products only to government intelligence and law enforcement agencies for the sole purpose of preventing and investigating terror and serious crime," the company says on its website. "Our vetting process goes beyond legal and regulatory requirements to ensure the lawful use of our technology as designed."
Human rights group Amnesty International, however, documents in detail how it traced compromised smartphones to NSO Group. Citizen Lab, a Canadian security organization at the University of Toronto, said it independently validated Amnesty International's conclusions after examining phone backup data.
In 2019, a study by the University of Toronto's Citizen Lab revealed that the Indian government was spying on lawyers, activists, and journalists using the Pegasus software via WhatsApp.
The Indian government had denied the allegations after WhatsApp filed a lawsuit against NSO in the United States, in which the messenger app confirmed the details reported by Citizen Lab.
The Washington Post, another member of the consortium, reported that 10,000 phone numbers on the list were from Mexico, belonging to politicians, union representatives, journalists, and government critics.
One of them was a Mexican freelance journalist who was murdered at a carwash. His cellphone was never found, and it could not be confirmed if it was infected with Pegasus.
Why is Pegasus in the news now?
 |
| Photo Getty |
Forbidden Stories, a Paris journalism nonprofit, and Amnesty International, a human rights group, shared with 17 news organizations a list of more than 50,000 phone numbers for people believed to be of interest to NSO customers.
The news sites confirmed the identities of many of the individuals on the list and infections on their phones. Of data from 67 phones on the list, showed 37 exhibited signs of Pegasus installation or attempted installation, according to The Washington Post. Of the 37, 34 were Apple iPhones.
How is Pegasus different from other spyware?
Pegasus aka Q Suite, marketed by the NSO Group aka Q Cyber Technologies as “a world-leading cyber intelligence solution that enables law enforcement and intelligence agencies to remotely and covertly extract” data “from virtually any mobile devices”, was developed by veterans of Israeli intelligence agencies.
Until early 2018, NSO Group clients primarily relied on SMS and WhatsApp messages to trick targets into opening a malicious link, which would lead to infection of their mobile devices. A Pegasus brochure described this as Enhanced Social Engineering Message (ESEM). When a malicious link packaged as ESEM is clicked, the phone is directed to a server that checks the operating system and delivers the suitable remote exploit.
In its October 2019 report, Amnesty International first documented use of ‘network injections’ which enabled attackers to install the spyware “without requiring any interaction by the target”. Pegasus can achieve such zero-click installations in various ways. One over-the-air (OTA) option is to send a push message covertly that makes the target device load the spyware, with the target unaware of the installation over which she anyway has no control.
This, a Pegasus brochure brags, is “NSO uniqueness, which significantly differentiates the Pegasus solution” from any other spyware available in the market.
What kind of devices are vulnerable?
 |
| Photo Fuzzy Skunk |
All devices, practically. iPhones have been widely targeted with Pegasus through Apple’s default iMessage app and the Push Notification Service (APNs) protocol upon which it is based. The spyware can impersonate an application downloaded to an iPhone and transmit itself as push notifications via Apple’s servers.
In August 2016, the Citizen Lab, an interdisciplinary laboratory based at the University of Toronto, reported the existence of Pegasus to cyber security firm Lookout, and the two flagged the threat to Apple. In April 2017, Lookout and Google released details on an Android version of Pegasus.
In December 2020, a Citizen Lab report flagged how government operatives used Pegasus to hack 37 phones belonging to journalists, producers, anchors, and executives at Al Jazeera and London-based Al Araby TV during July-August 2020, exploiting a zero-day (a vulnerability unknown to developers) against at least iOS 13.5.1 that could hack Apple’s then-latest iPhone 11. While the attack did not work against iOS 14 and above, the report said the infections it observed were probably a minuscule fraction of the total attacks, given the global spread of the NSO Group’s customer base and the apparent vulnerability of almost all iPhone devices prior to the iOS 14 update.
Does the spyware always get into any device it targets?
Usually, an attacker needs to feed the Pegasus system just the target phone number for a network injection. “The rest is done automatically by the system,” says a Pegasus brochure, and the spyware is installed in most cases.
In some cases, though, network injections may not work. For example, remote installation fails when the target device is not supported by the NSO system, or its operating system is upgraded with new security protections.
Apparently, one way to dodge Pegasus is to change one’s default phone browser. According to a Pegasus brochure, “installation from browsers other than the device default (and also chrome for android based devices) is not supported by the system”.
In all such cases, installation will be aborted and the browser of the target device will display a pre-determined innocuous webpage so that the target does not have an inkling of the failed attempt. Next, an attacker is likely to fall back on ESEM click baits. All else failing, says the brochure, Pegasus can be “manually injected and installed in less than five minutes” if an attacker gets physical access to the target device.
How Pegasus infects phones?
Over the years, Pegasus has evolved in the way it operates and infects devices. The first version of the spyware was detected in 2016 and used spear-phishing to infect a smartphone. This means that it worked through a malicious link, usually sent to the target through a bogus text message or an email. The device became infected as soon as the link was clicked.
It now adopts a different and more sophisticated approach for reaching new targets. Shockingly, the new method does not require any input from the target user. It can infect a device by what is called a "zero-click" attack.
An example of this was seen earlier in 2019, when WhatsApp blamed Pegasus for infecting more than 1,400 phones through a simple WhatsApp call. Due to a zero-day vulnerability, the malicious Pegasus code could be installed on the phone, even if the target never answered the call.
While this was fixed by WhatsApp, which also filed a case against NSO Group in the US, Pegasus has now acquired different capabilities.
| In a recent report, the Guardian highlights the use of a similar zero-click Pegasus attack that exploits Apple's iMessage. The report explains that exploiting undiscovered security lapses in such widely used services helps Pegasus infect many devices easily. |
The infections are apparently carried out by downloading malicious code from servers that NSO Group runs. The analysis by Amnesty International shows the links for downloading the bits of Pegasus are hidden in the contents of a message, or an image or the background data that apps often download on phones without requiring any inputs from users.
The fresh reports note that when the details of these servers become public, NSO Group shuts them down and creates new servers. In recent months, according to the reports, NSO Group is even using servers managed by cloud computing providers like Amazon Web Services to deliver Pegasus to phones.
READ MORE: What is Five Eye cybersecurity tools?
How is Pegasus detected on the phone?
Make no mistake that Pegasus is highly sophisticated spyware. This means that other than the intended spying purposes, it has been explicitly designed to avoid detection. So finding it on an infected device is no child's play.
In the earlier Pegasus attacks, the malicious link through the messages or emails were indicative enough of the spyware's presence. The consecutive practice of spyware-triggering WhatsApp calls was also identified as a threat later on.
How to get rid of Pegasus?
Cybersecurity experts have indicated that a device infected by Pegasus might never be able to recover from it completely. Traces of the spyware might still be found, even after a hard factory reset of the device.
So the best option for victims of the spyware attack is to get rid of the infected device altogether. Users can check for all the indicators of a compromise through Amnesty International's GitHub. In addition, the organisation has also released a modular tool, called Mobile Verification Toolkit (MVT) for such an analysis. Anyone finding traces of Pegasus on their phones should switch to a new phone and change the passwords of the applications and services they used on it.
Theoretically, astute cyber hygiene can safeguard against ESEM baits. But when Pegasus exploits a vulnerability in one’s phone’s operating system, there is nothing one can do to stop a network injection. Worse, one will not even be aware of it unless the device is scanned at a digital security lab.
Switching to an archaic handset that allows only basic calls and messages will certainly limit data exposure, but may not significantly cut down infection risk. Also, any alternative devices used for emails and apps will remain vulnerable unless one forgoes using those essential services altogether.
Therefore, the best one can do is to stay up to date with every operating system update and security patch released by device manufacturers, and hope that zero-day attacks become rarer. And if one has the budget, changing handsets periodically is perhaps the most effective, if expensive, remedy.
Since the spyware resides in the hardware, the attacker will have to successfully infect the new device every time one changes. That may pose both logistical (cost) and technical (security upgrade) challenges. Unless one is up against unlimited resources, usually associated with state power.
| Are there any rules to protect me? There is little meaningful legal protection against being targeted by spyware in most of the world. NSO says Pegasus cannot be used on numbers inside the United States, Israel’s most important ally. The United States has some legal restrictions on spyware, including the federal Computer Fraud and Abuse Act, which was enacted in 1986 and bans “unauthorized access” of a computer or phone, but its vague language has meant that it’s often unevenly applied in court. Some states have passed cybersecurity and privacy laws, such as California’s Comprehensive Computer Data Access and Fraud Act, which bans electronic tampering or interference. WhatsApp has cited both laws in an ongoing court case against NSO. Are there things I can do to make myself safer? There are cybersecurity basics that make people somewhat safer from hacks of all sorts. Keep your devices and their software up to date, preferably by activating “automatic updates” on your settings. Devices over five years old — especially if they are running outdated operating systems — are particularly vulnerable. Use a unique, hard-to-guess password for each device, site and app you use, and avoid easily predictable ones based on your phone number, date of birth or the names of your pets. A password manager such as LastPass or 1Password can make that easier. You should also turn on “two-factor authentication” everywhere you can: Those sites will ask not just for your password but for a second code, either sent to your phone or accessible via a separate authenticator app. Avoid clicking on links or attachments from people you don’t recognize. Whenever possible, activate “disappearing messages” or similar settings so communications automatically vanish after a set period of time. Who else can help protect my privacy? The entities with the most power to thwart spyware are probably makers of devices and software, such as Apple and Google. They have been improving security on their smartphone operating systems for years — but not enough to entirely thwart Pegasus and similar malware. Giant “cloud computing” companies can also take action to prevent their servers from helping the attacks: Both Microsoft and Amazon Web Services say they have taken steps to block malware when they’ve learned their systems were being used to transmit it. |
French probe after Pegasus spyware complaints
The Paris prosecutor's office opened a probe on Tuesday into allegations by investigative news website Mediapart and two of its journalists that they had been spied on by Morocco using the Pegasus spyware, Reuters report.
An investigation published on Sunday by 17 media organisations, led by the Paris-based non-profit journalism group Forbidden Stories, said the spyware, made and licensed by Israeli company NSO, had been used in attempted and successful hacks of 37 smartphones belonging to journalists, government officials.
Mediapart said in a series of tweets on Monday that Morocco's secret services had used Pegasus to spy on the mobile phones of two of its reporters.
Morocco has published an official statement rejecting what it called "unfounded and false allegations". NSO also denies any wrongdoing.
According to Reuters, the Paris prosecutor's statement does not mention Morocco and says only that it has decided to open the probe after receiving the complaint from Mediapart and its reporters.
Hungary issued a similar repudiation.
"The government has no knowledge of this type of data collection," Foreign Minister Peter Szijjarto told a press conference, adding that Hungary's civilian intelligence agency did not use the Pegasus software "in any way", according to France24 and AFP.
 Who is Natalia Fadeevy on 'Thirst Trap' TikTok Posted by Israeli Soldiers Who is Natalia Fadeevy on 'Thirst Trap' TikTok Posted by Israeli Soldiers TikTok is, in no doubt, popular right now. Israeli Defense Forces soldiers have taken advantage of TikTok to post thirst traps. Israeli soldiers are trying ... |
 Facebook Account Is Hacked: How To Solve, Best Ways to Protect Facebook Account Is Hacked: How To Solve, Best Ways to Protect Facebook is a big social platform, and there is thousands of accounts, which it will be always a possibility that your account will be ... |
 Netflix Got Hacked And E-Mail Changed – How To Get Account Back Netflix Got Hacked And E-Mail Changed – How To Get Account Back If you're concerned that your Netflix account has been maliciously accessed, here's how to claim back control. |