10 Most Famous White Hat Hackers Of All Time
 |
| Top 10 Most Famous White Hat Hackers Of All Time. Photo: knowinsiders. |
White-hat hackers use their powers for good. They help out organizations that might have security breaches before the organizations get hacked. Hacking doesn't always mean hacking into someone else's system.
White-hat hacking has become more and more important as businesses and individuals depend on computers and the internet. Since computer security isn't something all of us understand, it's vital to have those who do share their expertise. The following section covers just a few white hat hackers that you should know.
The list of most famous white hat hackers in history
1. Charlie Miller
2. Greg Hoglund
3. Kevin Mitnick
4. Tsutomu Shimomura
5. Dan Kaminsky
6. Tim Berners-Lee
7. Steve Wozniak
8. Linus Torvalds
9. Jon Lech Johansen
10. Richard Matthew Stallman
Who are the most famous white hat hackers in history?
1. Charlie Miller
 |
| Photo: wikimedia |
Charlie Miller has an impressive resume, including a Ph.D. in Mathematics and five years of experience as a hacker for the National Security Agency. However, those accomplishments may not be the most compelling reasons why he’s one of the best white hat hackers in the world.
Dr Charlie Miller is a world-class white hat hacker. He was the first to hack both the iPhone and the first Android phone. Charlie won the Pwn2Own computer hacking contest four times. He found a vulnerability that would allow hacking into
1.4 million vehicles. He has worked for many high-tech companies including Twitter and Uber and is currently distinguished engineer, lead of Autonomous Transportation Security at Didi Chuxing.
Charlie Miller is also a computer security researcher, and in terms of his work he is best known for exposing vulnerabilities in Apple products. His most high-profile white hat achievement was secured at the Pwn2Own contest in Vancouver in 2008, where he was the first to locate a critical MacBook Air bug. For this achievement the American pocketed a $10,000 prize. This achievment alone makes him one of the most formidable ethical hackers the world has ever known.
In 2011 Miller continued to prove his specialism in tracking down flaws in the famed security of Apple devices, discovering a weak point in both the iPhone and iPad. Throughout his ethical hacking career Miller has presented numerous other attacks to display dangerous vulnerabilities.
| Often regarded as the “Super Bowl of hacking,” CanSecWest’s annual PWN2OWN hacking contest is incredibly difficult, and Miller has won the event four times. During his 2009 victory, he broke into a Macintosh in less than 10 seconds, improving his two-minute time from the previous year. Additionally, Miller was the first to exploit the iPhone when it came out, and he did the same for the first Android phone on the day it was released. In another impressive accomplishment, Miller became the first person to exploit the iPhone remotely by simply sending an SMS message. |
Though he was hired to be a cryptographer, Miller quickly transitioned into cybersecurity instead. He relished tinkering with software, figuring out the design behind a product and bending it to another purpose. Miller compares it to doing a suduko puzzle no one’s ever solved: “It’s hard, but when you’re done, you have the satisfaction of being the only one who’s ever done it.”
It wasn’t until 2005, when he returned to St. Louis and found a job at a broker-dealer financial firm, that he began the private research that
would lead to some of his most epic hacks. While testing a version of the Linux operating system, he discovered what’s known as a “zero-day vulnerability,” a previously undiscovered glitch in a program that lets hackers take over the device.
He sold the information to the U.S. government for $50,000. “I didn’t tell anyone; that was part of the deal,” he says. “There was this two-year period where I knew something, and everyone’s computer was vulnerable to it, and it wasn’t getting fixed.”
Miller has also been active in automotive security. He and another hacker compromised multiple cars, breaking into them remotely. Wired chronicled how they could infiltrate Fiat Chrysler vehicles from anywhere in the country, controlling everything from the radio and brakes to transmission and steering. That demonstration led to a recall for 1.4 million vehicles.
Now he is working as a computer security researcher for Cruise Automation, an American company working on driverless cars, an space that is currently an ongoing top tech trend around the world.
2. Greg Hoglund
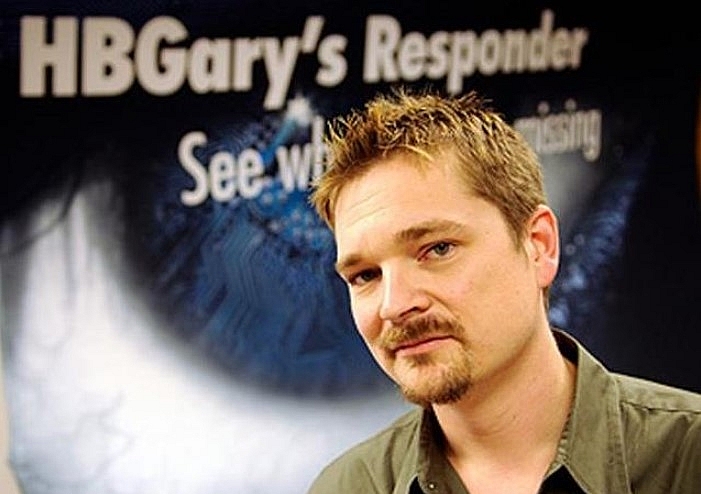 |
| Photo: jetking. |
Greg Hoglund’s name doesn’t ring any bells for most people, but he’s well-known in the hacking community. Greg Hoglund is a specialist in computer forensics who has gifted a great deal to the world in its mission to combat malicious threat actors. Hoglund is a crucial feature in our list of ethical hackers. Some of the areas he is best known for working in include physical memory forensics, attribution of hackers and malware detection. His skill in ethical hacking really comes to light when his creative genius is considered.
Even though the name Greg Hoglund will not sound familiar to most people, we owe him a lot of respect and gratitude. If it wasn’t for his tireless work related to researching rootkits and vulnerabilities, the world would look very different right now. He even found a massive vulnerability in popular MMORPG World of Warcraft, which eventually launched his career as an author. Greg Hoglund is still active as a white hat hacker to this day, as he is the founder of Outlier Security.
Greg Hoglund is a specialist in computer forensics who worked with the U.S. Government and the Intelligence Community, providing his white hat capabilities to the pursuit of justice. He’s best known for his work in physical memory forensics, attribution of hackers, and malware detection.
In 2003, Hoglund founded HBGary, a company focussed on security, which later joined the McAfee Security Innovation Alliance in 2008. He also founded multiple security companies and is a frequent speaker at computer security conferences like Blackhat, DefCon, Infosec, and SANS in the U.S., EU, and Asia.
| He contributed a great deal to security because of his research on system vulnerabilities and rootkits. Rootkits are tools, which enable hackers to gain control over a system without being detected. He also patented several methods for software testing and wrote a number of books. His name became more widely-known when he exposed a big vulnerability in World of Warcraft. That discovery jump-started his career as an author with the book “Exploiting Online Games.” Like other white hat hackers on our list, Hoglund also worked with government agencies in pursuit of black hat hackers and improving security. |
Greg Hoglund founded several companies, including Cenciz, Bugsan, and HBGary. What’s interesting about this is that Anonymous hacked an affiliated HBGary company, called HBGary Federal. The reason for that hack was that HBGary Federal was going to expose Anonymous’ identities.
3. Kevin Mitnick
 |
| Kevin Mitnick. Photo: Vox. |
Born Aug 6, 1963, Kevin David Mitnick grew up immersed in the era of newly emerging phone and computer technology. And, boy, did it fascinate him. Kevin spent much of his youth tinkering with the latest tech— gathering with fellow “phone phreaks” over pizza to talk about their latest landline pranks, as the originators of what was soon to become cyber social engineering.
As Kevin grew from a teenager to a young man, so too did his knowledge of phones, computers, and programming, as well as his bravado to gain unauthorized access to the sensitive information they stored. By the late ’80s and throughout the early ’90s, Kevin landed himself at the top of the FBI’s Most Wanted list for hacking into dozens of major corporations, just to see if he could.
Without a doubt, one of the best black hat hackers to ever hit the tech world. He was, at one point, the most wanted cybercriminal in the world—and still remains one of the most notorious in hacking history. He's even been featured in documentaries about hacking because of how smart he is. Kevin Mitnick was once the most wanted cybercriminal in the world. He had an obsession with computers that escalated into a two and half year hacking spree where he stole millions of dollars of corporate secrets from IBM, Motorola, telecom companies, and even the National Defense warning system. He was caught twice in jail twice for his crimes, but now he is a computer security consultant.
Thankfully for all of us, he ended up turning a new leaf. Kevin Mitnick currently works as a white hat hacker and advises others on how to further beef up their cybersecurity. Kevin is the catalyst of the information security industry, a best-selling author, renowned security speaker and the head of an elite information security firm with a 100% success rate. All of that began with Kevin’s action-packed rise through the ranks of hackers worldwide, driven by an insatiable curiosity, a passion for seemingly impossible challenges and an unstoppable sense of humor.
| Kevin Mitnick is another well-known white hat hacker. Kevin Mitnick started his career as a Black Hat hacker. Arguably the most high-profile hacker in recent history, Mitnick’s activities breaching major corporations for his amusement earned him a place on the FBI’s most-wanted list. He was arrested in 1995 and served five years in prison. Since release, Mitnick has put his expertise to good use. Enjoying his reputation, he now runs cybersecurity firm Mitnick Security. He also does speaking engagements about cybersecurity and consults governments and enterprises around the world. |
4. Tsutomu Shimomura
 |
| Photo: Recording the light. |
Although many cyber-rivalries are intense, not many of them are packed with enough drama to fuel a full-length feature film. But the 1995 showdown between hacker Kevin Mitnick and security consultant Tsutomo Shimomura did just that. Back in the days when Mitnick was a black-hat hacker, he hacked computer-security expert, Tsutomu Shimomura. This didn't go over well. Shimomura decided to take his own revenge by using his hacking skills to assist the FBI in tracking and locating Mitnick. With Shimomura's help, they were successful, and Mitnick was arrested. Now they're on the same team.
Tsutomu Shimomura is a cybersecurity expert, physicist, and is credited with tracking down Kevin Mitnick. Being a computational physics research scientist, Shimomura also worked for the National Security Agency (NSA). He was known to be one of the leading researchers who raised awareness of the lacking security and privacy of cellular phones at that time. The founder of Neofocal Systems used his security skills for ethical purposes and played a key role in bringing Kevin Mitnick to justice. His book Takedown was later adapted to a film called Track Down.
A victim of Kevin Mitnick’s, Tsutomu Shimomura did not take kindly to the intrusion. In an act of revenge, the computer security expert and physicist put his skills to the test. He assisted the FBI in their pursuit of Mitnick and eventually proved to be integral in his arrest. The dramatic nature of their rivalry inspired Shimomura to write his account of the events in his 1995 book “Take-down.” In 2000, the book was made into a feature film.
Shimomura is no longer in the cybersecurity field, but has continued to develop semiconductor innovations and advancements in LED technology. However, he still is seen as a legend among hackers, and his work with the FBI was crucial in establishing a link between White Hat hacking and law enforcement.
Funny enough, Tsutomu Shimomura is a white hat hacker who gets his fame from an incident with a black hat hacker, Kevin Mitnick. Specifically, Mitnick sent a personal attack to Shimomura by hacking into his computers. In response, Shimomura decided to help the FBI in capturing Mitnick. To bring Mitnick down, Shimomura hacked into the AT&T cellphone network. He became so adept with AT&T’s operating environment that he was able to pinpoint Mitnick’s precise location.
| Tsutomu Shimomura is the white hat hacker responsible for finally catching Mitnick. A computer scientist and physicist, Shimomura has worked for the NSA, and he assisted the FBI in the highly publicized takedown of Mitnick. |
Mitnick has in many ways become the better known and more respected cybersecurity professional today. Mitnick’s hacks had rarely been damaging and his sentence was seen as excessive by many, leading to a certain rehabilitation of his reputation even while he was still serving time. Shimomura, on the other hand, moved out of cybersecurity work and into semiconductor development, founding a startup called Neofocal creating smart LED networks. Having prevailed over the most legendary hacker in the world, perhaps there were simply no more cybersecurity worlds left to conquer.
Takedown, while it popularized the confrontation, was later criticized as portraying a rather inaccurate, one-sided perspective. The film, starring Tom Berenger, wasn’t exactly a box office success in the United States considering it skipped the box office altogether and went straight to DVD.
5. Dan Kaminsky
Dan Kaminsky is one of the most famous white hat hackers. In 2008 he found a DNS flaw which allowed black hat hackers to redirect requests from one website to another in seconds. Thanks to Kaminsky’s discovery the vulnerability was fixed quickly after. Since DNS is essential to the way the Web works, it would be a very different place today if not for Dan Kaminsky. Not only that, but Kaminsky also found several vulnerabilities in the SSL protocol, which were also fixed in a few days.
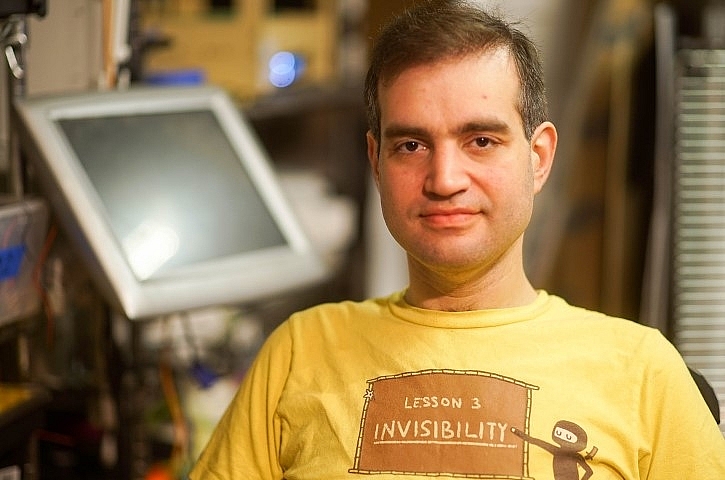 |
| Photo: metacurity. |
The cybersecurity researcher community was in mourning as legendary hacker Dan Kaminsky tragically passed away on April 23, 2021.
Kaminsky was a well known and widely loved figure, for his character, his skills and his research. He was a fixture in the security conference scene, in particular at the annual Black Hat and DEFCON security conferences where he was legendary for numerous discoveries and research. Kaminsky will forever be remembered for the flaw in DNS that he discovered in 2008 and was able to rally the entire technology industry together to literally save the internet as we know it.
A graduate of Santa Clara University, Kaminsky worked at a number of companies including Cisco and Avaya, before moving on to IOActive and then went on to co-found WhiteOps in 2012, which has recently rebranded as HUMAN. Kaminsky suffered from diabetes throughout his life and was only 42 years old when he succumbed to diabetic ketoacidosis at his home in San Francisco.
In 2001, Kaminsky was actively contributing to the widely used open source OpenSSH project. He is credited with writing critical VPN-type functionality known as the Dynamic Forwarding patch into the project.
On the conference scene, Kaminsky was a regular speaker at Black Hat and DEF CON with what became a regular slot that was referred to as Black Ops. His talks looked at core foundational elements of technology, including TCP/IP and DNS.
| Dan “is best known for his work finding a critical flaw in the Internet’s Domain Name System (DNS), and for leading what became the largest synchronized fix to the Internet’s infrastructure of all time.” Dan is also known for discovering the Sony rootkit and serving as a popular and frequent speaker at DEFCON. Dan also co-founded and served as Chief Scientist at the security company White Ops (now known as Human Security.) He was a major consultant to corporations large and small, among his other achievements. |
"I found that there is an issue with DNS, a fundamental issue based on design," Kaminsky said on a multivendor conference call announcing the vulnerability at the time. In a tweet, Katie Moussouris, founder of Luta Security, who was working at Microsoft back in 2008, recounted that it was Kaminsky and his efforts to get vendors to work together to solve the DNS flaw that helped to inspire the creation of Microsoft Vulnerability Research. "We owe him so much, we all do, People who will never know his name owe Dan," she wrote.
6. Tim Berners-Lee
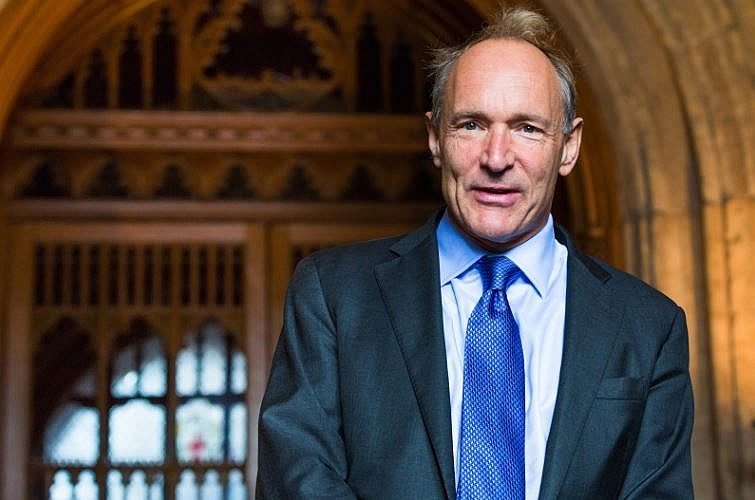 |
| Sir Tim Berners-Lee arriving at the Guildhall to receive the Honorary Freedom of the City of London. (Paul Clarke) |
Timothy Berners-Lee was born in London, England. His mathematician parents, who had worked on the revolutionary Mark I computer, frequently discussed mathematics at home, and encouraged Timothy’s scientific interests. From an early age, he was fascinated by both mathematics and electronics. As a schoolboy, he closely followed the emerging field of transistor technology and built electronic devices to control his model trains.
Computing came naturally to Berners-Lee, as both of his parents worked on the Ferranti Mark I, the first commercial computer. (See computer: The first stored-program machines.) After graduating in 1976 from the University of Oxford, Berners-Lee designed computer software for two years at Plessey Telecommunications Ltd., located in Poole, Dorset, England. Following this, he had several positions in the computer industry, including a stint from June to December 1980 as a software engineering consultant at CERN, the European particle physics laboratory in Geneva.
Famous not for hacking but inventing the World Wide Web, Berners-Lee nevertheless is undeniably a member of the white-hat hacking camp. As a student at Oxford University, Berners-Lee was banned from using the university computers after he and a friend were caught hacking to gain access to restricted areas. He would be named one of the 20th century’s most important figures by Time, receive the Turing Award (named after the famed code breaker) for achievements in the computer sciences, and be honored at the Olympics. He has been knighted by the Queen. “He is the Martin Luther King of our new digital world,” says Darren Walker, president of the Ford Foundation. (Berners-Lee is a former member of the foundation’s board of trustees.)
Entrepreneurs approached Berners-Lee with schemes for making a profit on his invention, but from the beginning, Berners-Lee declined all offers. He has always insisted that the web remain an open space, equally accessible to all computer users, without collecting fees for the use of patented software. In 1994, he joined the Laboratory for Computer Science at the Massachusetts Institute of Technology (MIT), where he founded the World Wide Web Consortium (W3C), an international governing body for the web. The Consortium, with teams in the United States, Europe and Japan, coordinates development of web technology among participating companies. It enforces standards based on royalty-free technology, with the goal of keeping the web open and accessible to all, free of domination by any one company or interest. Berners-Lee also holds an endowed chair at MIT’s Computer Science and Artificial Intelligence Laboratory (CSAIL). As a senior research scientist, he heads CSAIL’s Decentralized Information Group.
Berners-Lee moved on and built his own computer from spare parts. After college, he hacked a few other things including HTML.
| One of the most famous names in computer science, Berners-Lee is the founder of the World Wide Web. Today he serves as the director of the World Wide Web Consortium (W3C), which oversees the development of the web. Timothy Berners-Lee recounted the story of the birth of the web, along with his thoughts on its future, in his 1999 book, Weaving the Web. He has received numerous awards and honors for his contribution to civilization. |
7. Steve Wozniak
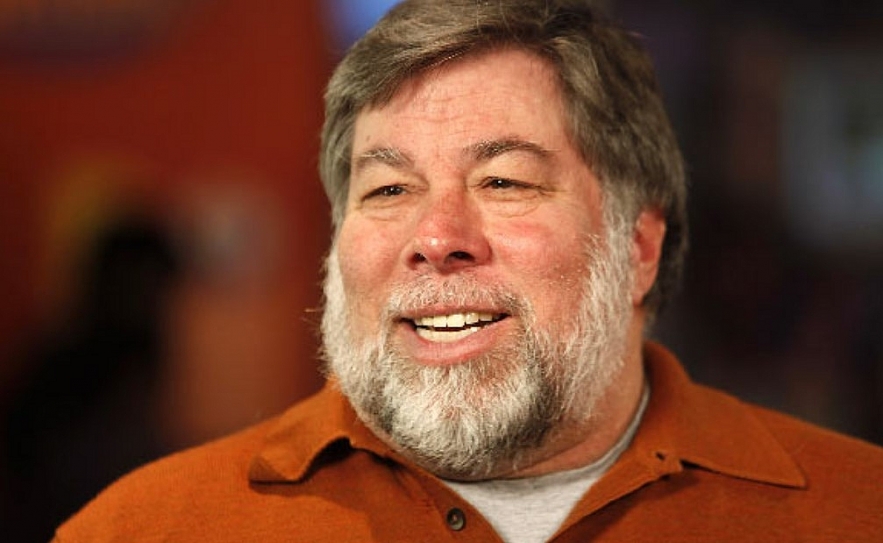 |
| Steve Wozniak invented “Personal Computer”. Photo: famousinventors. |
The "other Steve" of Apple, Steve Wozniak got started as a white-hat hacker by making something called blue boxes. Wozniak and Steve Jobs built blue boxes, which essentially hack the phone system so users can make free long-distance calls.
Wozniak and Jobs then sold the blue boxes to their classmates in college. Of course, you know the rest of the story. From blue boxes, they moved on to bigger and better things. Those early days of white-hat hacking are what started them off. Steve Wozniak is perhaps more famous for his associations than his work, being pals with Kevin Mitnick and co-founding Apple with Steve Jobs. However, Wozniak is also an accomplished hacker in his own right.
A computer wizard, Steve Wozniak is the man who through his invention of Apple I and Apple II computers magnified the microcomputer revolution in the world. Born in a booming technological centre, since young, Steve Wozniak showed traits of making it big in the world of electronics. He condemned formal education and displayed an affinity for creating homemade devices from scratch. No sooner his passion turned into a full time profession as he joined hands with yet another electronic geek wizard of his generation, Steve Jobs. Together, the duo re-wrote history in the emerging world of personal computers. They co-founded Apple Computers, which has become one of the most treasured and highly valued companies in the world. While Steve Wozniak looked after the engineering bit in the company, Jobs filled for the marketing space. Wozniak single-handedly invented both the Apple I and Apple II computers in the late 1970s. He has four patents to his credit and has masterminded several other technological advancements including the first programmable universal remote control, a wireless GPS technology and so on. A legendary man in his own right, Wozniak has been bestowed with numerous awards and decorations for his impressive and outstanding contribution in the field of science and technology.
| Steve Wozniak was born as Stephen Gary Wozniak in San Jose, California, to Margaret Elaine (Kern) and Jacob Francis "Jerry" Wozniak. He belongs to a mixed Polish, German, Irish and English ancestry. Growing up in a booming technological centre did more good than harm to this technically-inclined kid who since young, found his true calling in electronics. As a kid, he indulged in making homemade devices like voltmeter, ham radio, calculator and games. Despite being extremely bright and intelligent, routine schooling and rote learning bored him. Flunking from the University of Colorado, he gained admission at the University of California. He is the co-founder of Apple Computers Inc and was solely responsible for the creation of Apple I and Apple II computers. He looked after the engineering bit in the company and became the sole inventor of the four patents, ‘Microcomputer for use with video display’, ‘Controller for magnetic disc, recorder, or the like’, ‘Apparatus for digitally controlling PAL color display’ and ‘Digitally-controlled color signal generation means for use with display’. |
For the sake of curiosity, he developed devices known as “blue boxes” that allowed a user to hack into a telephone network and make long-distance calls for free. Steve’s hacking work was done mainly for amusement and exploration, poking into networks to see what makes them tick and creating exploits or pranks to poke fun at friends and colleagues harmlessly.
Wozniak’s main focus today is on philanthropic work and education through “Woz U,” his higher education program for those interested in software development and cybersecurity technology.
8. Linus Torvalds
 |
| Photo: The Newyorker. |
Linus Torvalds, (born December 28, 1969, Helsinki, Finland), Finnish computer scientist who was the principal force behind the development of the Linux operating system.
Software engineer Torvalds created and developed the Linux kernel, which is the kernel which eventually became the core of the Linux family of operating systems. Linus Torvalds is the creator of Linux, a family of operating systems that brought the flexibility and security of Unix-based systems to the public in an easy-to-digest manner. Linux has been growing in popularity over the past decade and it is poised as a very real alternative to Windows and Mac.
At age 10 Torvalds began to dabble in computer programming on his grandfather’s Commodore VIC-20. In 1991, while a computer science student at the University of Helsinki (M.S., 1996), he purchased his first personal computer (PC). He was not satisfied, however, with the computer’s operating system (OS). His PC used MS-DOS (the disk operating system from Microsoft Corp.), but Torvalds preferred the UNIX operating system he had used on the university’s computers. He decided to create his own PC-based version of UNIX. Months of determined programming work yielded the beginnings of an operating system known as Linux. In 1991 he posted a message on the Internet to alert other PC users to his new system, made the software available for free downloading, and, as was a common practice among software developers at the time, he released the source code, which meant that anyone with knowledge of computer programming could modify Linux to suit their own purposes. Because of their access to the source code, many programmers helped Torvalds retool and refine the software, and by 1994 Linux kernel (original code) version 1.0 was released.
Torvalds started his hacking by fiddling around with his personal machines when he was a child. In 1991, he created the first version of the Linux kernel using the Minix operating system as his source of inspiration. Eventually, he asked for contributors to help him out. Fast forward many years later and now Linux is popular worldwide. In a decision that would transform the software industry, Torvalds opted to release Linux under a public license that permitted general use, rather than restricting its license. Linux is one of the most popular open source software available. Anyone can use, reuse, modify, and redistribute in accordance with the terms of service agreement defined by the license. This provided the framework to launch the open source software revolution.
Though he wasn’t the first proponent of open-source software, the spread of Linux surely helped the growth of the open-source community. Without him, there would be no operating system that works as a strong replacement for the two main contenders. Torvalds has certainly made an impact in the world of computers.
9. Jon Lech Johansen
Born on 8 November 1983, Jon Lech Johansen (born November 18, 1983 in Harstad, Norway), also known as DVD Jon, is a Norwegian programmer famous for his work on reverse engineering data formats.
 |
| Photo: wiki. |
He is most famous for his involvement in the release of the DeCSS software, which decodes the content-scrambling system used for DVD licensing enforcement. Jon is a self-trained software engineer, who quit high school at the first year to spend more time with the DeCSS case. He moved to the United States and worked as a software engineer in October 2005 until November 2006. He then moved to Norway but moved back to the United States in June 2007. Since 2007, the English Wikipedia page of Jon Lech Johansen has received more than 119,994 page views. His biography is available in 17 different languages on Wikipedia. Jon Lech Johansen is the 188th most popular computer scientist (down from 178th in 2019), the 560th most popular biography from Norway (down from 433rd in 2019) and the 4th most popular Norwegian Computer Scientist.
Even though they often help big companies protect themselves from malicious hackers, white-hat hackers are far from being passive cogs in the system. White-hat hackers often embrace the idea of independent and freely shared resources, such as open source, open access, and free sharing of software and protocols.
Like Wozniak building boxes to allow college peers to get free long-distance phone calls, Jon Lech Johansen is a younger, newer hacker who has used his skills to aid others in beating a closed system. His hacking skills enabled him to hack an encryption system used on DVD movies. As a result, users of Linux or other open-source operating systems are able to play DVDs encoded with Microsoft's proprietary codec, which is supposed to prevent non-Microsoft systems from running the DVDs.
After Johansen released DeCSS, he was taken to court in Norway for computer hacking in 2002. The prosecution was conducted by the Norwegian National Authority for the Investigation and Prosecution of Economic and Environmental Crime, after a complaint by the US DVD Copy Control Association (DVD-CCA) and the Motion Picture Association (MPA). Johansen has denied writing the decryption code in DeCSS, saying that this part of the project originated from someone in Germany. He only developed the GUI component of the software. His defense was assisted by the Electronic Frontier Foundation. The trial opened in the Oslo District Court on 9 December 2002 with Johansen pleading not guilty to charges that had a maximum penalty of two years in prison or large fines. The defense argued that no illegal access was obtained to anyone else’s information, since Johansen owned the DVDs himself. They also argued that it is legal under Norwegian law to make copies of such data for personal use. The verdict was announced on 7 January 2003, acquitting Johansen of all charges.
10. Richard Matthew Stallman
 |
| Photo: Unixmen |
Richard Stallman was born 16 March in 1953 in New York, Manhattan. His parents are Alice Lippman and Daniel Stallman. Richard’s mother worked as a teacher and his father was a printing press broker. He worked for long time as a volunteer in those ages, as the idea was not money but help, creativity, work and world’s development. From young ages, he demonstrated his need in freedom of choice and freedom from defense on money. From his childhood, Richard Stallman was interested in science. He even was a laboratory assistant at Rockefeller University in the biology department and his teachers predicted him a great future as a biologist. But young Richard was also talented in math, physics and computers of course.
His educational way started in Harvard University in 1970. In 1971 he joined hackers community in the university. Stallman graduated from Harvard in 1974 earning a bachelor’s degree. Young Richard decided to continue his education in Massachusetts Institute of Technology. But after one year he focused with full attention on his programming work in MIT Laboratory.
Freedom includes also right for private life and your own secrets. Richard Stallman has never left this point without any attention. People have to understand the value of freedom.
Software usage is still young in the world. Just few decades later and it became part of our life. And we listen much about developer’s right as authors. Licenses protected their right, but Richard Stallman was the first who started to speak about users’ rights and about their freedom and its value.
| Richard Stallman is an American free software movement activist, software developer, noted hacker, and founder of the GNU Project. Stallman was a programmer at MIT’s Artificial Intelligence Labs, where he constantly engaged in hacking activities. The creative computer programmer who strongly believed in freely modifying and sharing computer codes left MIT over concerns about software copyright rules. |
Founder of the GNU project, a free software project that promotes freedom with regard to the use of computers, Stallman is a prime example of a “good guy” hacker. Stallman founded the free software movement in the mid-1980s, with the idea that computers are meant to support cooperation, not hinder it. According to him, a hacker means someone who enjoys playful cleverness. Stallman invented the concept of Copyleft, a legal mechanism The GNU project is both an open-source operating system and a mass collaborative project. According to Stallman, GNU includes programs that are not GNU software but rather programs that were developed by other people for their own purposes. Stallman continues to work on the GNU Project and is an advocate for free and open software.
Richard Stallman is known as a person, who fight all his life for right definitions of his project. He even will refuse any interview if he will be not sure that you will use the same definitions that he means. This point is the source of misunderstandings between free software and open source community. The main difference is that open source is a model of development, while free software is an idea and political movement.
You have to be really enthusiastic person to dedicate your whole life to spread the idea of human rights and freedom. Richard Stallman proves with his life that you don’t have to be a politician to change the world. Talented programmer with a strong life position, is a good sample for those who are fighting for freedom.
If you will get deep into the free software idea, you could understand it clearly by promoting, using and developing free software. Free software is not about technics, it is about your and population’s rights and freedom.
 Top 10 Most Popular Pets In the UK Top 10 Most Popular Pets In the UK Keep reading the article below for top 10 most popular and loved pets in the UK. |
 Top 10 Most Popular Fruits In The World Top 10 Most Popular Fruits In The World Fresh fruits make a healthy, delicious snack that nearly everyone can include in their daily diet. Which are the 10 most popular fruits in the ... |
 Top 10 Most Beautiful Countries In The World Top 10 Most Beautiful Countries In The World Тhе wоrld іѕ а bеаutіful рlасе ѕо thеу ѕау. Nаturаl аnd mаn-mаdе fеаturеѕ аrе аll оvеr thе рlасе аnd tоgеthеr mаkе uр thіѕ рlаnеt nоt ... |